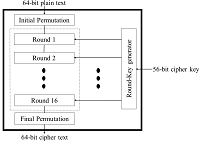
Secure Intrusion Detection System for MANETs Using Triple-DES Algorithm
Keywords:
Mobile Adhoc Network (MANET), Intrusion Detection System (IDS)Abstract
Networking is the process of accessing, exchanging or sharing the information. Packet switching plays a vital role in data transfer. Compared to wired network, wireless network has more data transferring. MANETs and WSN are the most common forms of Wireless media; in MANETs nodes are deployed or distributed in Ad-hoc way and they are communicating or exchange message using wireless Transmission. Security is a measure concern in Mobile Ad-hoc Network because MANETs have wide distribution of node and open medium; therefore, it becomes vulnerable and is easy for malicious hackers to attack.
Published
How to Cite
Issue
Section
License
Submission of a manuscript implies: that the work described has not been published before that it is not under consideration for publication elsewhere; that if and when the manuscript is accepted for publication. Authors can retain copyright of their article with no restrictions. Also, author can post the final, peer-reviewed manuscript version (postprint) to any repository or website.

Since Oct. 01, 2015, PETI will publish new articles with Creative Commons Attribution Non-Commercial License, under The Creative Commons Attribution Non-Commercial 4.0 International (CC BY-NC 4.0) License.
The Creative Commons Attribution Non-Commercial (CC-BY-NC) License permits use, distribution and reproduction in any medium, provided the original work is properly cited and is not used for commercial purposes