Hybrid RSA–SHA-256 Scheme for Enhancing Physical-Layer Security in MIMO-OFDM Systems Using SDR Implementation
DOI:
https://doi.org/10.46604/aiti.2026.15667Keywords:
MIMO-OFDM, RSA, SHA-256, subcarrier scrambling, physical layer securityAbstract
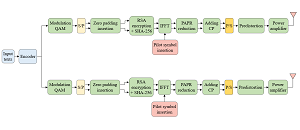
This research aims to enhance the physical-layer security (PLS) of multi-input multi-output orthogonal frequency division multiplexing (MIMO-OFDM) wireless communication systems. The proposed method integrates Rivest–Shamir–Adleman (RSA)-based subcarrier index scrambling with secure hash algorithm (SHA)-256 hashing to ensure both confidentiality and integrity without altering the transmitted waveform. The scheme is implemented on a 2×2 Universal Software Radio Peripheral (USRP)-based MIMO-OFDM software-defined radio (SDR) testbed and evaluated using symbol distribution analysis, bit-error-rate (BER) performance, and security assessment. Experimental results indicate that RSA-based scrambling substantially increases symbol randomness while preserving Shannon-consistent BER performance across multiple modulation orders, with minimal penalty in signal-to-noise ratio (SNR). Additionally, security analysis demonstrates that the combination of RSA-2048 and SHA-256 is resistant to Wiener’s attack and the common modulus attack, thereby supporting efficient and secure real-time MIMO-OFDM communication.
References
H. A. Hussein Al-Delfi and F. S. Hasan, “Hybrid Ciphering and Frequency Domain Scrambling for Secure Speech Transmission through MIMO-OFDM System,” International Journal of Intelligent Engineering and Systems, vol. 15, no. 6, pp. 563-575, 2022.
Z. Guo, B. Liu, J. Ren, Y. Mao, X. Wu, S. Chen, et al., “High Security and Low Complexity SCMA-OFDM Transmission System Based on Dual Three-Dimensional Memory Hyperchaotic in Seven-Core Optical Fibers,” Journal of Lightwave Technology, vol. 42, no. 16, pp. 5458-5465, 2024.
M. M. Banat, J. Bas, and A. A. Dowhuszko, “Improved Physical-Layer Security for OFDM Using Data-Based Subcarrier Scrambling,” IEEE Globecom Workshops, pp. 1-6, 2021.
M. M. Hasan, M. Cheffena, and S. Petrovic, “Physical-Layer Security Improvement in MIMO OFDM Systems Using Multilevel Chaotic Encryption,” IEEE Access, vol. 11, pp. 64468-64475, 2023.
A. Mukherjee, S. A. A. Fakoorian, J. Huang, and A. L. Swindlehurst, “Principles of Physical Layer Security in Multiuser Wireless Networks: A Survey,” IEEE Communications Surveys & Tutorials, vol. 16, no. 3, pp. 1550-1573, 2014.
S. Golstein, T. H. Nguyen, F. Horlin, P. D. Doncker, and J. Sarrazin, “Physical Layer Security in Frequency-Domain Time-Reversal SISO OFDM Communication,” International Conference on Computing, Networking and Communications, pp. 222-227, 2020.
M. L. F. Abbade, W. S. Souza, M. O. Santos, I. E. L. Rodrigues, I. Aldaya, L. H. Bonani, et al., “Discrete Spectral Encryption of Single-Carrier Signals with Pseudo Random Dynamic Keys,” IEEE Transactions on Information Forensics and Security, vol. 19, pp. 4914-4929, 2024.
R. P. Hudhajanto, I. G. P. Astawa, and A. Sudarsono, “Covert Communication in MIMO-OFDM System Using Pseudo Random Location of Fake Subcarriers,” EMITTER International Journal of Engineering Technology, vol. 4, no. 1, pp. 150-163, 2016.
Z. Weng, J. Ren, B. Liu, Y. Mao, X. Wu, X. Song, et al., “Physical Layer Security Scheme for Key Concealment and Distribution Based on Carrier Scrambling,” Optics Express, vol. 32, no. 9,pp. 15053-15064, 2024.
M. Li, G. Zhang, G. Li, H. Li, and X. Zhang, “Secure Transmission Algorithm Based on Subcarrier Sorting and XOR Operation in OFDM Systems,” IEEE International Conference on Communication Systems, pp. 147-151, 2018.
D. Ramakrishna and M. A. Shaik, “A Comprehensive Analysis of Cryptographic Algorithms: Evaluating Security, Efficiency, and Future Challenges,” IEEE Access, vol. 13, pp. 11576-11593, 2025.
X. Liang, C. Zhang, Y. Luo, X. Wang, and K. Qiu, “Secure Encryption and Key Management for OFDM-PON Based on Chaotic Hilbert Motion,” Journal of Lightwave Technology, vol. 41, no. 6, pp. 1619-1625, 2023.
H. Mohammed and D. Saha, “Encrypted-OFDM: A Secured Wireless Waveform,” Computer Networks, vol. 255, article no. 110871, 2024.
A. A. E. Hajomer, X. Yang, and W. Hu, “Secure OFDM Transmission Precoded by Chaotic Discrete Hartley Transform,” IEEE Photonics Journal, vol. 10, no. 2, pp. 1-9, 2018.
J. Ayad, A. Sadiq, B. Makki, Z. A. Abbood, H. J. Abdulkareem, and Z. K. Hussein, “Secure Images Transmission through OFDM System,” 2nd International Conference on Computing and Machine Intelligence, pp. 1-4, 2022.
A. Dash, A. Sarkar, A. Chatterjee, S. Darshana, M. Pandey, and R. K. Barik, “Multi-Factor Analysis of RSA Based on Variations in Primes Used for Modulus Generation,” 3rd International Conference on Innovative Sustainable Computational Technologies, pp. 1-6, 2023.
Z. Wang, “Secure Image Transmission in Wireless OFDM Systems Using Secure Block Compression-Encryption and Symbol Scrambling,” IEEE Access, vol. 7, pp. 126985-126997, 2019.
N. Kaur, A. Mittal, U. K. Lilhore, S. Simaiya, S. Dalal, K. Saleem, et al., “Securing Fog Computing in Healthcare with a Zero-Trust Approach and Blockchain,” EURASIP Journal on Wireless Communications and Networking, vol. 2025, no. 1, article no. 5, 2025.
N. Karnik, A. Kumar, P. Mahajan, A. Srivastav, S. Das, and B. Singh, “An Efficient Technique for Securing a Multi-Cloud Storage Environment,” International Journal of System Assurance Engineering and Management, in press. https://doi.org/10.1007/s13198-025-02751-2
Z. M. Yahya and M. F. Al-Gailani, “Secure Data Delivery in a Software-Defined Wireless Body Area Network,” Journal of Telecommunications and Information Technology, no. 2, pp. 41-47, 2024.
R. Acheampong, D. M. Popovici, T. Balan, A. Rekeraho, and M. S. Ramos, “Enhancing Security and Authenticity in Immersive Environments,” Information, vol. 16, no. 3, article no. 191, 2025.
D. M. Acasamoso, A. M. Sison, and R. P. Medina, “Enhancing Data Security with RSA-SHA 256: Mitigating Timing Attacks,” 15th International Conference on Information and Communication Technology Convergence, pp. 574-578, 2024.
M. M. Ahmed and S. H. Alnajjar, “Cipher Text to Secure Li-Fi System Using Hybrid Encryption Algorithm,” Iraqi Journal for Computer Science and Mathematics, vol. 6, no. 2, article no. 16, 2025.
K. Baskar, K. Muthumanickam, P. Vijayalakshmi, and S. Kumarganesh, “A Strong Password Manager Using Multiple Encryption Techniques,” Journal of The Institution of Engineers (India): Series B, vol. 106, no. 4, pp. 1207-1214, 2025.
U. Gulen and S. Baktir, “Side-Channel Resistant 2048-Bit RSA Implementation for Wireless Sensor Networks and Internet of Things,” IEEE Access, vol. 11, pp. 39531-39543, 2023.
H. Dymova, “Study of Cryptographic Security of Computer Networks,” Computer-Integrated Technologies: Education, Science, Production, no. 57, pp. 15-19, 2025. (In Ukrainian)
C. Gilbert and M. Gilbert, “Exploring Secure Hashing Algorithms for Data Integrity Verification,” SSRN Electronic Journal, in press. https://doi.org/10.2139/ssrn.5251606
M. Zheng, “Revisiting Small Private Key Attacks on Common Prime RSA,” IEEE Access, vol. 12, pp. 5203-5211, 2024.
Published
How to Cite
Issue
Section
License
Copyright (c) 2026 M Wisnu Gunawan, I Gede Puja Astawa, Amang Sudarsono

This work is licensed under a Creative Commons Attribution-NonCommercial 4.0 International License.
Submission of a manuscript implies: that the work described has not been published before that it is not under consideration for publication elsewhere; that if and when the manuscript is accepted for publication. Authors can retain copyright in their articles with no restrictions. is accepted for publication. Authors can retain copyright of their article with no restrictions.
Since Jan. 01, 2019, AITI will publish new articles with Creative Commons Attribution Non-Commercial License, under The Creative Commons Attribution Non-Commercial 4.0 International (CC BY-NC 4.0) License.
The Creative Commons Attribution Non-Commercial (CC-BY-NC) License permits use, distribution and reproduction in any medium, provided the original work is properly cited and is not used for commercial purposes.